MD5SUM - Calculate and verify MD5 hash values for files. : Branko Lankester : Free Download, Borrow, and Streaming : Internet Archive

PPT – Short Chosen-Prefix Collisions for MD5 and the Creation of a Rogue CA Certificate PowerPoint presentation | free to view - id: 1f5be1-ZDc1Z

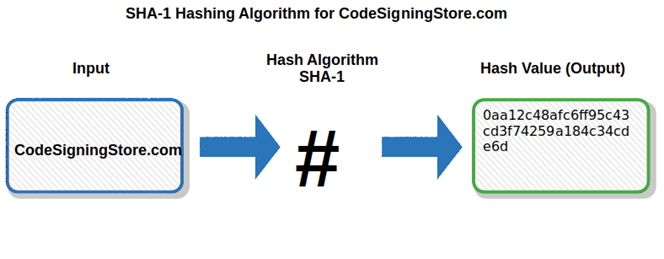
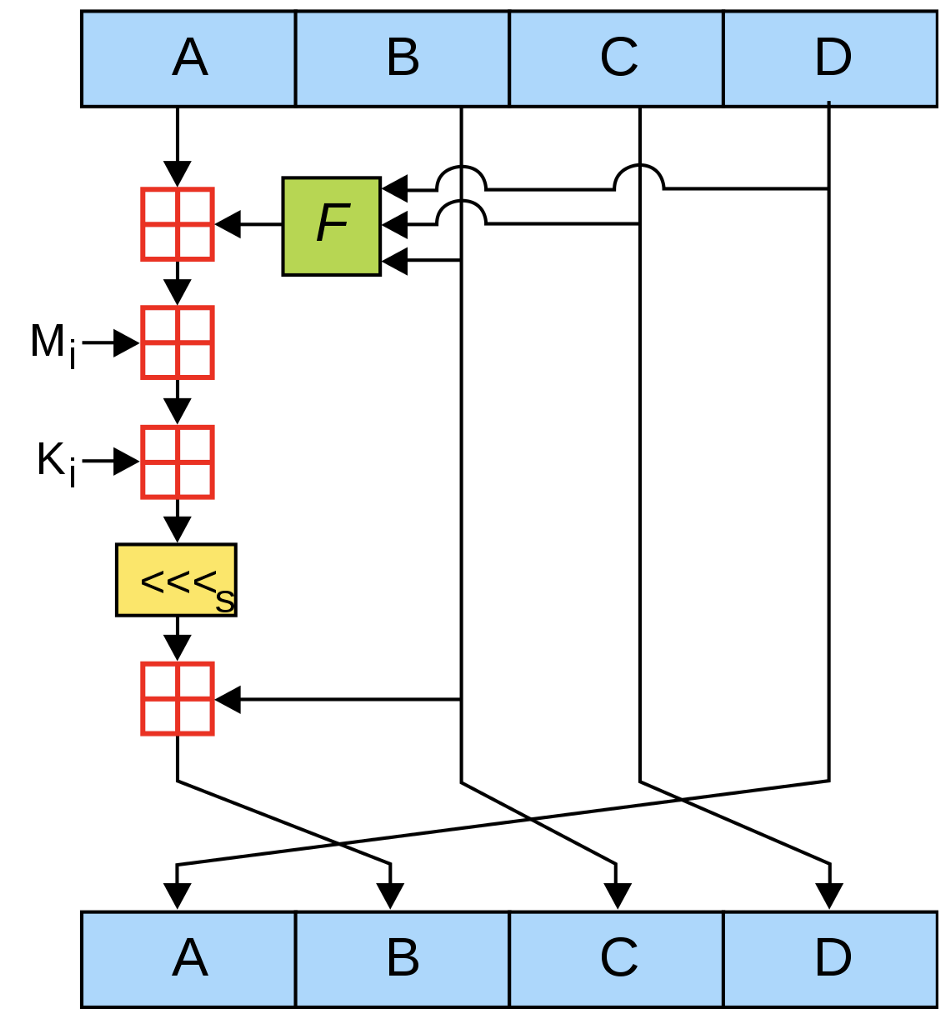
MD5 Generation Auto-Generated Slides To Visualize MD5 Hash Generation by Chris Fremgen. - ppt download